Install with vulsctl
Vulsctl
Linux Distributions
The following example should work on Fedora based Linux distributions, which include: CentOS, RedHat, Amazon Linux etc (tested on CentOS and Red Hat 7).
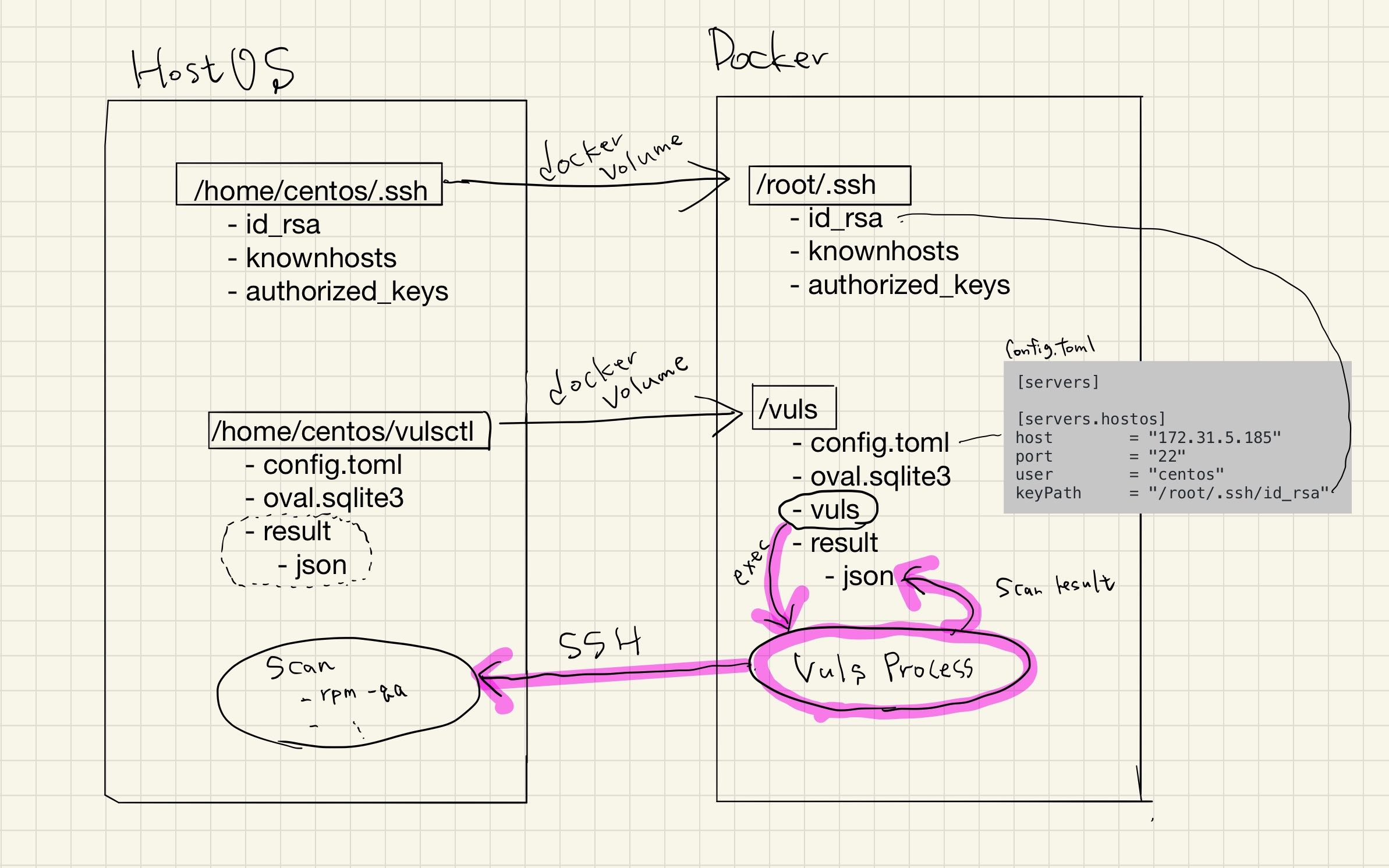
Vulsctl was created to ease setup. Each shell script is a wrapper around Docker commands.
Setup Docker
- Install Docker
- Dockerを非rootユーザで管理します。
$ sudo systemctl start docker
Vulsctl をクローン
$ git clone https://github.com/vulsio/vulsctl.git
$ cd vulsctl
Fetch Vulnerability Databases
This will take some time ...
$ cd docker
$ ./update-all.sh
Config, Scan, Report
Prepare the config.toml in the vulsctl install directory similar to the configuration below.
[servers]
[servers.hostos]
host = "52.10.10.10"
port = "22"
user = "centos"
# if ssh config file exists in .ssh, path to ssh config file in docker
sshConfigPath = "/root/.ssh/config"
# keypath in the Vuls docker container
keyPath = "/root/.ssh/id_rsa"
When config exists in .ssh, vuls refers to /root/.ssh/config in the docker container when connecting to SSH. However, an error occurs because the local user does not match the user in Docker. To deal with this, specify /root/.ssh/config in sshConfigPath.
The scan.sh will mount $HOME/.ssh from the host operating system into the Docker container, however you will need to SSH into the target server beforehand which will add your fingerprint to $HOME/.ssh/known_hosts.
` 
$ ssh [email protected] -i ~/.ssh/id_rsa.pem
$ ./scan.sh
$ ./report.sh
$ ./tui.sh
For details, see
Vulsrepo
$ ./vulsrepo.sh
$ docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
39c8830dbeac ishidaco/vulsrepo "vulsrepo-server" 3 seconds ago Up 1 second 0.0.0.0:5111->5111/tcp focused_wu
Vulsrepo is running on http://host-ip:5111.